Don't get hacked. Get Exploitr.
Exploitr provides cyber security services to help your organisation identify real cyber risk, ensure compliance, and make defensible decisions.
What We Do
Cyber Security Services
We help organisations identify cyber risk through independent, outcome-focused security testing of their applications, APIs, networks, cloud, and more.
Penetration Testing
Simulate real-world cyberattacks to identify exploitable vulnerabilities in your applications, infrastructure, and networks before attackers do.
Learn moreConfiguration Reviews
Identify misconfigurations in your cloud, network, or applications that could lead to security vulnerabilities and data breaches.
Learn moreContinuous Penetration Testing
Maintain ongoing security assurance with regular, scheduled penetration testing that adapts to your evolving environment and threat landscape.
Learn moreVulnerability Scanning
Automated vulnerability scanning to identify common security issues and misconfigurations across your applications, infrastructure, and networks.
Learn moreWhy Choose Exploitr
Quality testing. Expert guidance. No surprises.
Our penetration testing services are designed to uncover real, exploitable risks and provide organisations with clear guidance on how to fix them.
Direct access to your consultant, start to finish
From the first scoping conversation to the final debrief, you’ll deal with the consultant running your engagement and not an account manager or project coordinator acting as a go-between.
Scoped around your environment, not a standard template
Every engagement starts with a conversation about your specific systems, risk profile, and objectives. The scope, methodology, and deliverables are built around what you actually need.
Reports written for your audience
Every assessment includes a detailed technical report for the team responsible for remediation, and a clear executive summary for stakeholders who need to understand business risk without wading through technical detail.
Fixed pricing, agreed before we start
Every engagement is quoted at a fixed price before testing begins. No day rates, no scope creep, no surprises on the invoice.
The same standard of testing, regardless of your size
Whether you’re a ten-person startup or a thousand-person enterprise, every engagement receives the same methodology, the same reporting standard, and the same level of attention throughout testing.
Security visibility included as standard
Every engagement includes complimentary access to Attack Surface Center to provide a live view of findings as they’re discovered, and not just a static PDF at the end. Track, manage, and remediate vulnerabilities in one place, throughout and beyond your assessment.
Attack Surface Center
See vulnerabilities as they're discovered – not two weeks later in a PDF
Included with every engagement at no extra cost. While most firms send a PDF weeks after testing ends, Attack Surface Center gives you a live window into your assessment from day one.
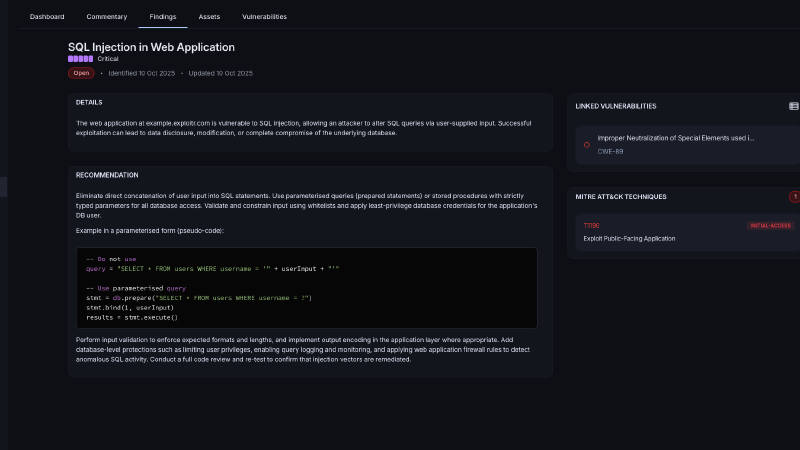
Interactive Reports
View your assessment reports within the platform directly. See your vulnerabilities as soon as they're discovered.
Learn more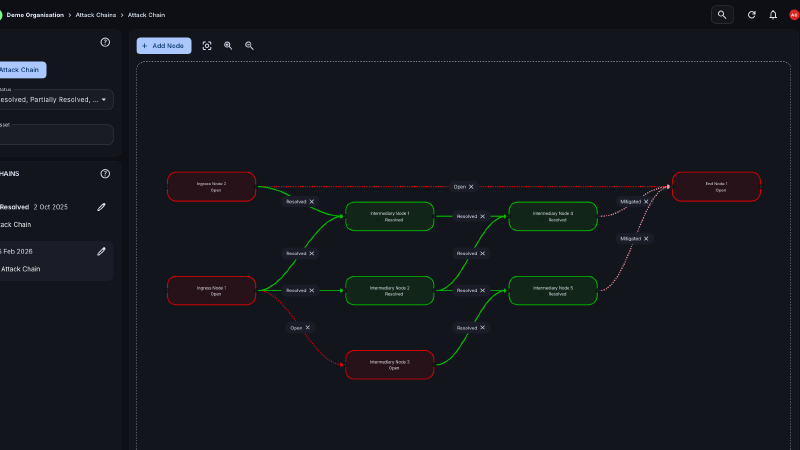
Attack Chains
See the paths to exploitation as we discover them. Mitigate and see the cyber kill chain in real-time.
Learn more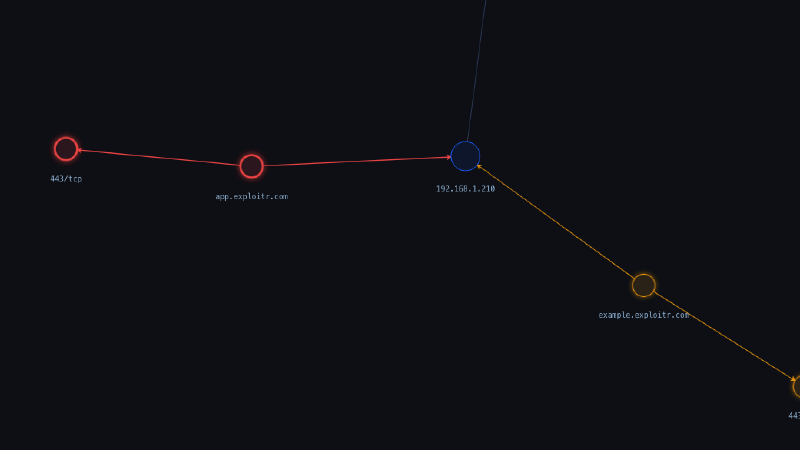
Attack Surface Map
Visualise your attack surface, see the assets at risk, and get the full picture.
Learn more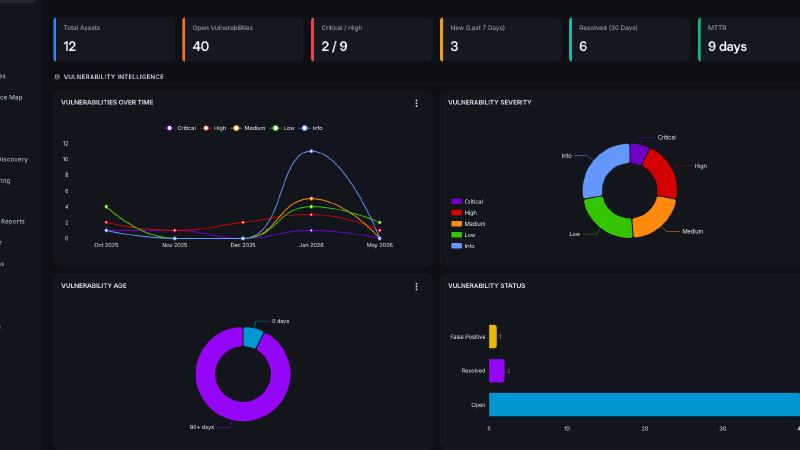
Explore the Attack Surface Center
Security visibility that doesn't end when testing does. Manage, track, and remediate findings in one place.
Learn more
