Articles
Whether you’re looking for in-depth analyses, practical guides, or the latest research findings - our content is intended to share our knowledge and expertise in the field of cyber security.
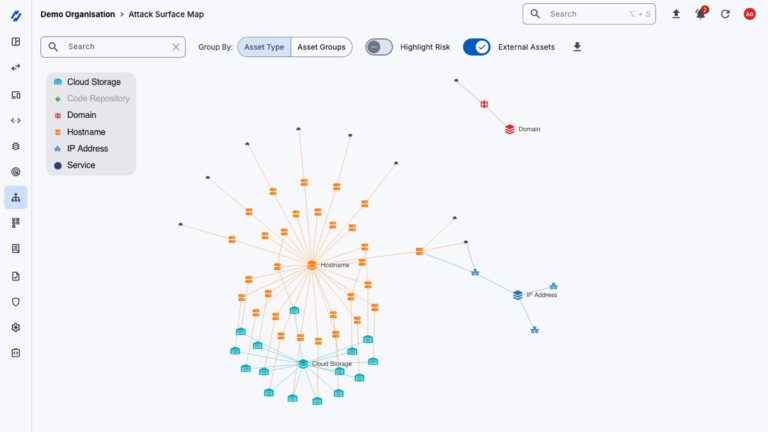
What is External Attack Surface Management (EASM)?
Common Vulnerability Management Challenges

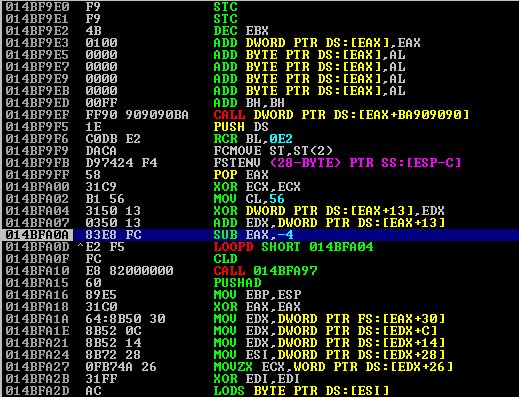
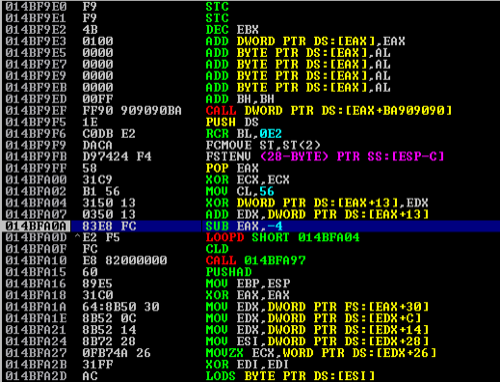
Manually Implanting Backdoors in PE Files
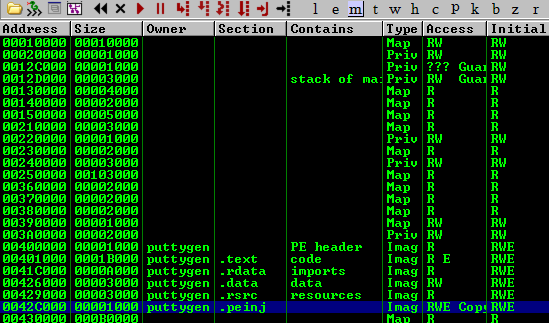
Using an Egghunter to Exploit Minimal Buffer Overflows
Cyber Essentials Certified

An Introduction in Exploiting Basic Vanilla Buffer Overflows