Desktop Application Security
Protecting Locally Installed Software
Desktop application security focuses on protecting software installed directly on end-user devices, such as Windows, macOS, and Linux applications. These applications can often run with elevated privileges, access local system resources, and handle sensitive data – making security flaws particularly high impact.
Unlike web applications, desktop software operates within the user’s operating system environment. Vulnerabilities can arise from insecure local storage, weak update mechanisms, excessive permissions, insecure design that could lead to local or remote code execution, or trusting local files, users, or processes without validation. These issues are rarely identified through network-based testing or automated tools alone.
Desktop application security testing assesses how an application behaves on a real system and how it could be abused by a malicious user or attacker. The goal is to identify vulnerabilities that could lead to data exposure, privilege escalation, or wider system compromise, and to provide clear guidance on reducing those risks.
Real-World Impact
These issues are rarely identified through network-based testing or automated tools alone. Manual testing is essential to discover how attackers could manipulate the application’s behavior, reverse engineer sensitive logic, or exploit trust assumptions.
Our testing methodology combines static analysis, dynamic analysis, and manual security review to identify vulnerabilities specific to desktop applications. We examine authentication mechanisms, local data storage, file permissions, update processes, and how the application interacts with the underlying operating system.
Where applicable, we also assess how the application interacts with backend APIs or services to ensure end-to-end security.
What We Test
Desktop application testing focuses on vulnerabilities specific to locally installed software and its interaction with the operating system.
Authentication and authorisation mechanisms
Local data storage and credential handling
Insecure file permissions and sensitive files
Update mechanisms and supply chain risks
Dynamic and static analysis
Input handling and memory safety issues
Use of insecure cryptography
Inter-process communication (IPC) flaws
Client-side logic and trust assumptions
Business logic flaws
Pricing
Pricing depends on application complexity, supported platforms, authentication mechanisms, and integration with external services. A fixed price is confirmed after a short scoping review.
Pricing Examples
Why Choose Exploitr
Our penetration testing services are designed to uncover real, exploitable risks and provide organisations with clear guidance on how to fix them.
Manual, consultant-led testing
Real security experts, not just automated tools. Get thorough analysis from experienced professionals.
Remediation advice tailored to you
Specific guidance for your business and tech stack with practical, actionable recommendations.
Standards-led testing methodology
Testing delivered with industry best practices and testing methodologies.
Direct communication
Talk directly with experienced testers throughout the engagement process.
Real-world testing
Testing aligned to actual attack patterns that matter to your business.
Transparent pricing
Know your costs upfront with transparent, fixed-price proposals.
Get the right level of testing
How Penetration Testing Works
Each penetration test follows a methodical, structured process to ensure that testing is safe, focused, and aligned with your environment. All work is scoped in advance and priced on a fixed basis.
Scoping
Every assessment starts by planning and agreeing the scope, objectives, and boundaries before testing begins.
Manual Testing
Hands-on testing that’s tailored to your systems and applications, not just automated scans.
Exploitation & Impact
Where appropriate, we safely action the exploitation of vulnerabilities to demonstrate what impact this may have to your organisation.
Reporting
Each report is created with your organisation in mind. We provide findings with detailed information, contextual remediation guidance, and an executive summary for your stakeholders.
Desktop Application Testing FAQs
We test applications across all major platforms including Windows (.exe, .msi), macOS (.app, .dmg), and Linux (various formats). This includes native applications, Electron-based apps, Java applications, .NET applications, and cross-platform frameworks.
Whether your application is distributed commercially, used internally, or delivered as enterprise software, we can assess its security.
No, source code is not required. We can perform black box testing with just the compiled application. However, white box testing (with source code access) provides more thorough coverage and can identify vulnerabilities earlier in the development lifecycle. We recommend white box testing when possible, especially for applications handling sensitive data.
Depending upon the agreed scope for testing, we can perform reverse engineering of the application to approach vulnerability discovery like an attacker would. In certain cases, such as with Windows .NET applications, we can attempt to reverse engineer local installations or portable executables to retrieve the source code.
We conduct testing in isolated environments using test accounts and sample data. We never test against production systems or real user data unless explicitly coordinated. Our testing focuses on identifying vulnerabilities without causing damage, and we maintain detailed logs of all testing activities.
Desktop application testing focuses on different attack vectors including: memory corruption vulnerabilities (buffer overflows), local privilege escalation, insecure local data storage, DLL hijacking, code injection, reverse engineering protection, and update mechanism security.
Unlike web applications that run in browsers with security sandboxes, desktop apps often have deeper system access and different trust boundaries.
Yes. For applications requiring specialised hardware, we can test on-site or you can provide remote access to a testing environment. For licensed software, you’ll need to provide valid licenses for our testing environment. We can also work with time-limited trial versions if full licenses aren’t available.
We test both standard user and administrative privilege scenarios. We specifically look for privilege escalation vulnerabilities where a standard user could gain administrative access. If your application requires admin privileges to run, we’ll assess whether this is truly necessary and test for vulnerabilities that could allow attackers to abuse those elevated privileges.
Basic reverse engineering is a standard part of desktop application testing to understand how the application works, identify hardcoded secrets, and find vulnerabilities. However, we respect intellectual property and only perform the level of analysis necessary for security testing. All findings remain confidential and we sign NDAs if required.
Yes, update mechanism security is a critical component of desktop application testing. We verify that updates are delivered over encrypted channels, properly signed, and cannot be intercepted or tampered with by attackers. Insecure update mechanisms are a common way attackers distribute malware to users.
We test the entire attack surface including client-side vulnerabilities and the security of communications with backend services. This includes API authentication, encrypted communications, certificate validation, and whether sensitive data is exposed through client-server communications. For comprehensive coverage, we may recommend combined desktop and API testing.
Get a free quote
Speak with our security team directly
Experts in providing thorough testing coverage
Professional services you can trust
Fixed pricing with no surprises
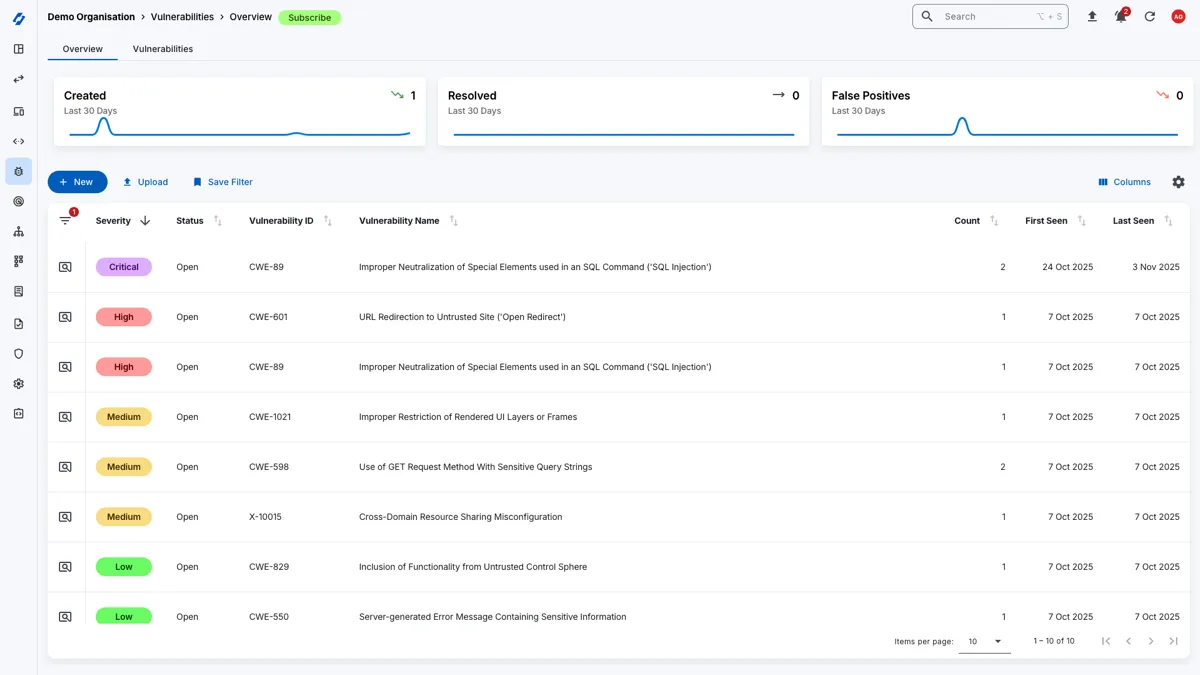
Attack Surface Management
Gain complementary access to the Attack Surface Center platform with your penetration test to manage your vulnerabilities, assets, and track remediation progress.