What Our Wi-Fi Testing Includes
Our Wi-Fi security testing involves an assessment of your organisation’s deployed Wi-Fi configuration, assessing the security of the access points and authentication controls, along with reviewing the deployment of endpoint device configuration for evil-twin and rogue access point exploitation.
This type of testing is crucial for identifying vulnerabilities that could be exploited by attackers who may be in range of your office Wi-Fi, or targeting portable devices out in the real-world.
WPA Authentication Weaknesses
802.1X Misconfiguration & Bypass
Rogue AP / Evil Twin Detection
Credential Capture & Cracking Attempts
Wireless Segmentation & Guest Isolation
Client Device Security & Misassociation Risks
Hidden SSID Disclosure & Broadcast Weaknesses
Internal Network Access from Wireless
Wireless Controller Security Review
Pricing
Pricing varies depending on the number of SSIDs, client density, building layout and testing complexity. All work is fully manual, exploitation‑led, and performed by experienced penetration testers.
Pricing Examples
Why Choose Exploitr
Our penetration testing services are designed to uncover real, exploitable risks and provide organisations with clear guidance on how to fix them.
Manual, consultant-led testing
Real security experts, not just automated tools. Get thorough analysis from experienced professionals.
Remediation advice tailored to you
Specific guidance for your business and tech stack with practical, actionable recommendations.
Standards-led testing methodology
Testing delivered with industry best practices and testing methodologies.
Direct communication
Talk directly with experienced testers throughout the engagement process.
Real-world testing
Testing aligned to actual attack patterns that matter to your business.
Transparent, fixed pricing
Know your costs upfront with transparent, fixed-price proposals.
Wi-Fi Testing FAQs
Wi-Fi security testing (also called wireless penetration testing) assesses the security of your wireless networks to identify vulnerabilities that could allow unauthorised access, eavesdropping, or attacks against connected devices. We test authentication mechanisms, encryption protocols, access point configurations, and the security of devices connected to your wireless network.
Yes, Wi-Fi testing requires physical presence since wireless signals are location-dependent. We’ll need to visit your office or facilities with our specialised equipment. Testing duration depends on the number of locations, but most engagements require at least 1 day on-site. For multi-location organisations, we can coordinate testing across sites.
Most testing activities are passive or low-impact and won’t affect normal operations. However, certain tests (like deauthentication attacks or attempting to capture handshakes) may cause brief, localised disruptions. We can perform this type of testing against a sample “device” (i.e. a provided representative laptop) for instances where this may cause an impact to business operations.
Yes, detecting unauthorised access points is a key component of Wi-Fi testing. We perform wireless sweeps to identify all access points broadcasting in your facility, including hidden SSIDs. We’ll identify which access points are authorised versus rogue devices that employees or attackers may have connected to your network.
Guest networks require special attention since they’re intentionally accessible to the general public or office visitors. We test that guest networks are properly isolated from corporate networks, captive portals cannot be bypassed, bandwidth and access controls are working, clients cannot attack other guest devices, and the guest network cannot be used as a pivot point to attack internal resources.
Yes, we can assess the security of devices connecting to your wireless network. This includes testing for vulnerabilities that could be exploited when connected to Wi-Fi (evil twin attacks, man-in-the-middle attacks) and whether devices are configured securely (automatic connection to unknown networks, vulnerable Wi-Fi drivers).
Wi-Fi testing focuses specifically on wireless access and the unique vulnerabilities of wireless protocols.
Internal network testing assumes you’re already connected to the network and focuses on what you can do once inside (lateral movement, privilege escalation, accessing sensitive data).
Many organisations benefit from both: Wi-Fi testing to secure the entry point, and internal network testing to secure what’s accessible once inside.
Get a free quote
Speak with our security team directly
Experts in providing thorough testing coverage
Professional services you can trust
Fixed pricing with no surprises
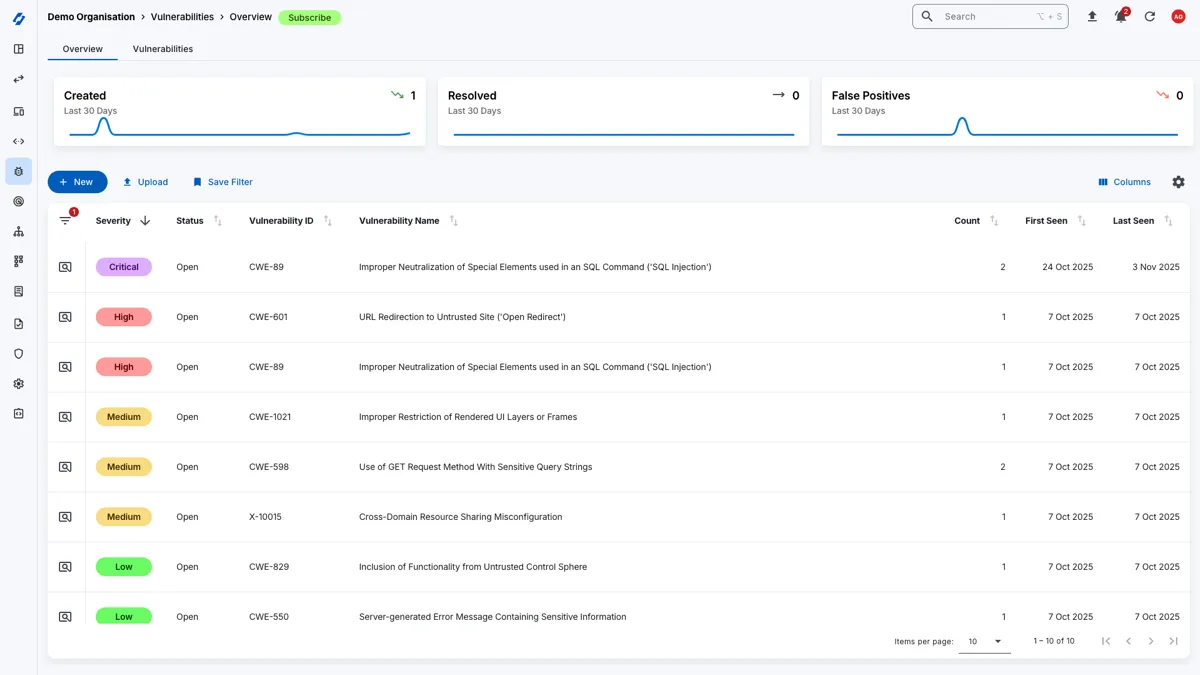
Attack Surface Management
Gain complementary access to the Attack Surface Center platform with your penetration test to manage your vulnerabilities, assets, and track remediation progress.