What is Vulnerability Scanning?
Vulnerability scanning is a process used to identify security weaknesses and vulnerabilities in computer systems, servers, networks, or applications. It…
Vulnerability scanning is a process used to identify security weaknesses and vulnerabilities in computer systems, servers, networks, or applications. It…
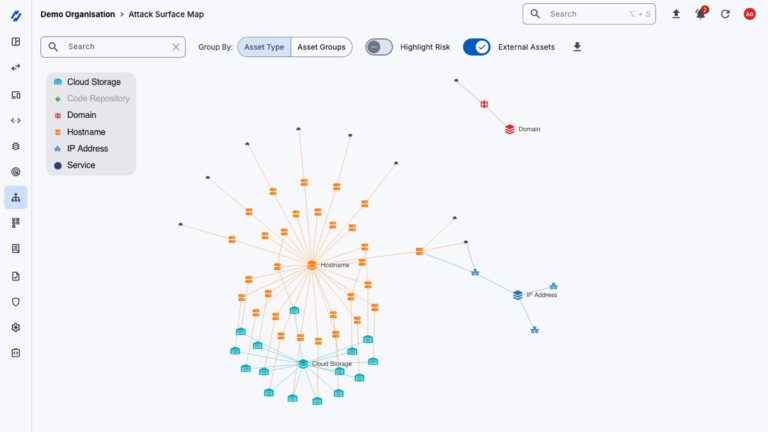
External Attack Surface Management (EASM) is the ongoing process of discovering, inventorying and monitoring all of an organisation’s externally facing…

There is much more to vulnerability management than running a scanner and applying every missing patch that gets reported. Done…
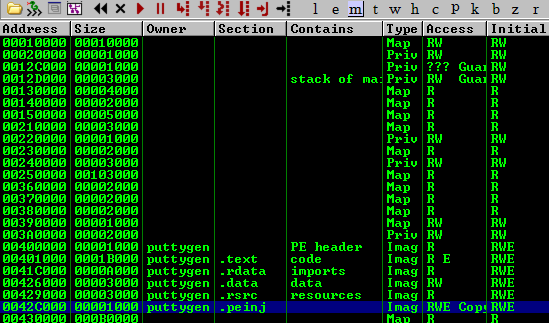
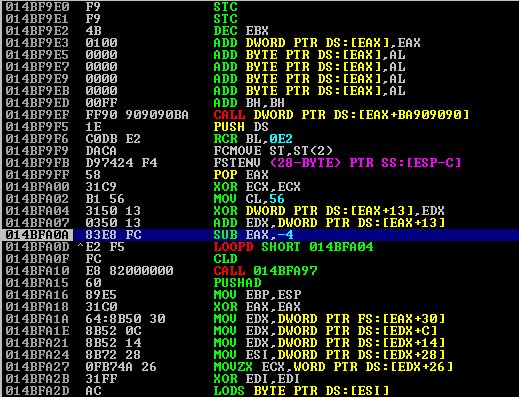
Tools like msfvenom, Veil (formerly Veil-Evasion), Shellter , and others automate shellcode injection into PE files. In this post, we’ll…
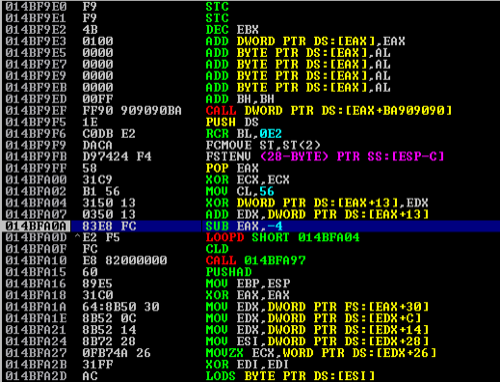
Following on from my previous blog post on basic buffer overflows, this article will delve into slightly more advanced exploitation…

Exploitr is proud to announce that we have achieved the Cyber Essentials certification, demonstrating our commitment to cybersecurity best practices…
A buffer overflow is a type of vulnerability that occurs when a program writes more data to memory than it…
The few weaknesses inherent within the authentication handshake process for WPA/WPA2 PSKs have been known for a long time. This…