OK, now it’s really time to disable Net-NTLMv1
The risks of poisoning attacks against Net-NTLMv1 have grown with the release of an 8.6TB rainbow table. Net-NTLMv1 isn’t fully…
The risks of poisoning attacks against Net-NTLMv1 have grown with the release of an 8.6TB rainbow table. Net-NTLMv1 isn’t fully…

Vibe coding is a modern day buzzword for prompt-driven, AI-assisted development. Over the last few years there has been an…

What is DKIM? DKIM (DomainKeys Identified Mail) is an email authentication method that allows a domain to sign its emails…

What is DMARC? DMARC (Domain-based Message Authentication, Reporting, and Conformance) is a security mechanism that works alongside SPF (Sender Policy…
SPF (Sender Policy Framework) is an email security mechanism that aims to mitigate email spoofing attacks, which is a common…
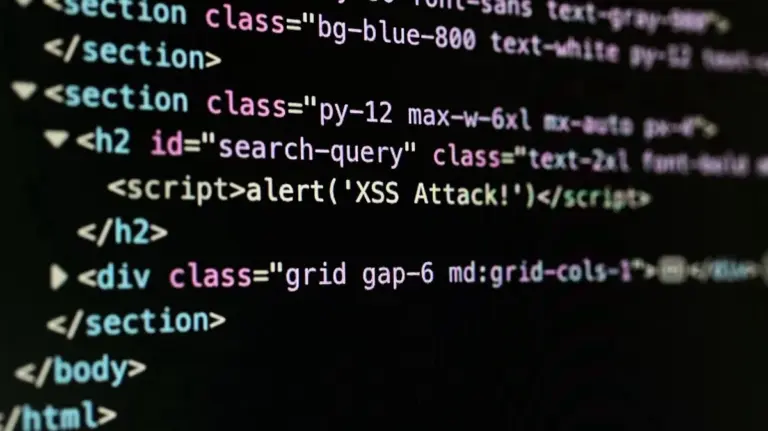
Cross-Site Scripting (XSS) is a common web application vulnerability (frequently in the OWASP Top 10) that can allow an attacker…

SQL injection (SQLi) is a critical application security vulnerability that could allow an attacker the ability to manipulate SQL queries…
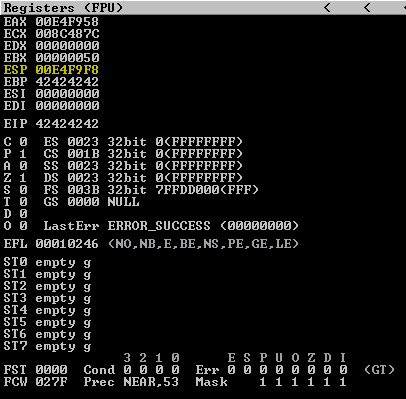
In exploit development, understanding and identifying bad characters is a crucial step in ensuring that your payloads function as intended.…

What is Phishing? Phishing is a type of social engineering cyberattack that uses email as a delivery method with an…