Cyber Essentials Certified

Exploitr is proud to announce that we have achieved the Cyber Essentials certification, demonstrating our commitment to cybersecurity best practices…

Exploitr is proud to announce that we have achieved the Cyber Essentials certification, demonstrating our commitment to cybersecurity best practices…
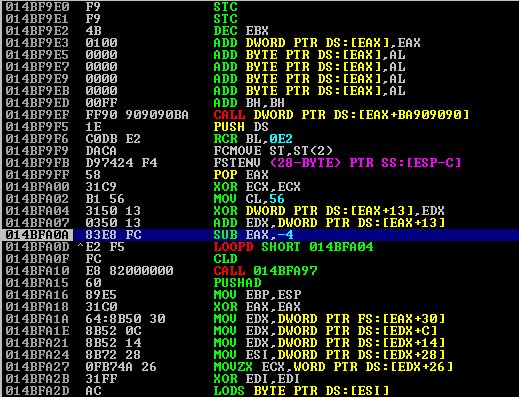
A buffer overflow is a type of vulnerability that occurs when a program writes more data to memory than it…
The few weaknesses inherent within the authentication handshake process for WPA/WPA2 PSKs have been known for a long time. This…