What is Password Cracking and How Does it Work?
Password cracking is the process of recovering the plaintext password from a cryptographic hash or encrypted password, often through the…
Password cracking is the process of recovering the plaintext password from a cryptographic hash or encrypted password, often through the…

We are excited to announce that Exploitr has taken a significant step in our commitment to excellence within the cybersecurity…
A red-team engagement is an advanced form of cybersecurity assessment where a team of ethical hackers, known as the red…
Penetration testing, sometimes known as “pen testing”, “pentesting”, or “ethical hacking”, is a cybersecurity practice in which ethical hackers simulate…
Vulnerability scanning is a process used to identify security weaknesses and vulnerabilities in computer systems, servers, networks, or applications. It…
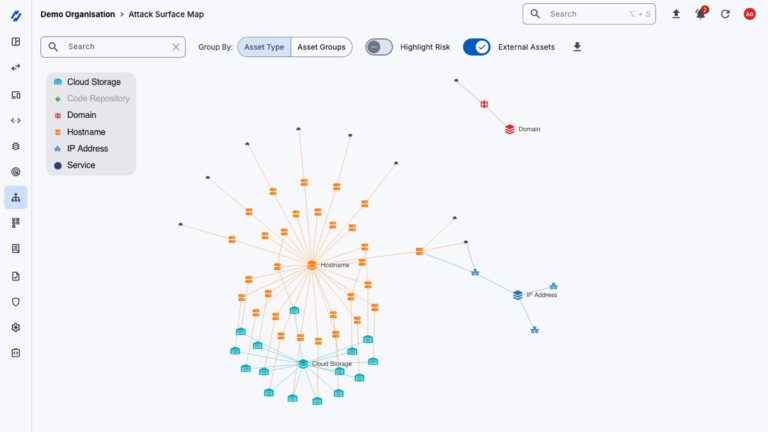
External Attack Surface Management (EASM) is the ongoing process of discovering, inventorying and monitoring all of an organisation’s externally facing…

There is much more to vulnerability management than running a scanner and applying every missing patch that gets reported. Done…
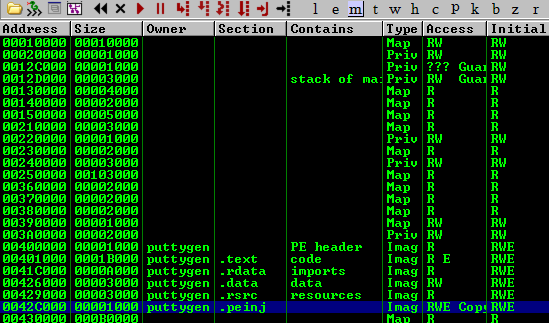
Tools like msfvenom, Veil (formerly Veil-Evasion), Shellter , and others automate shellcode injection into PE files. In this post, we’ll…
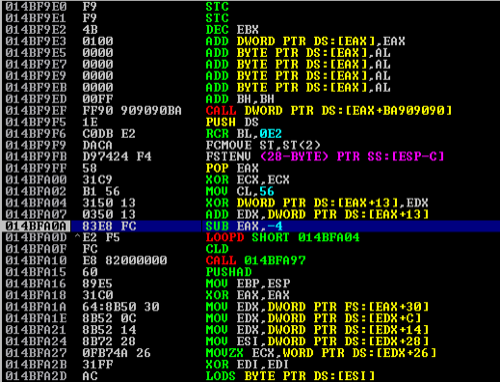
Following on from my previous blog post on basic buffer overflows, this article will delve into slightly more advanced exploitation…